Ask Terry Halvorsen, CIO of Samsung Electronics’ IT & Mobile Communication B2B Business, what he knows about Donald Trump’s smartphone and you’ll be met with a closed door, but ask him about his experience using Samsung Knox and he opens right up.
Formerly in the role of CIO at the U.S. Department of Defense, Halvorsen has enjoyed higher levels of national security clearance than your average CIO. But ask him about the U.S. President’s mobile device and he’s quick to seal his lips.
“I won’t comment on anything the President uses,” he says. “You could ask the White House.”
(It turns out that Trump switched to using an iPhone in March of last year.)
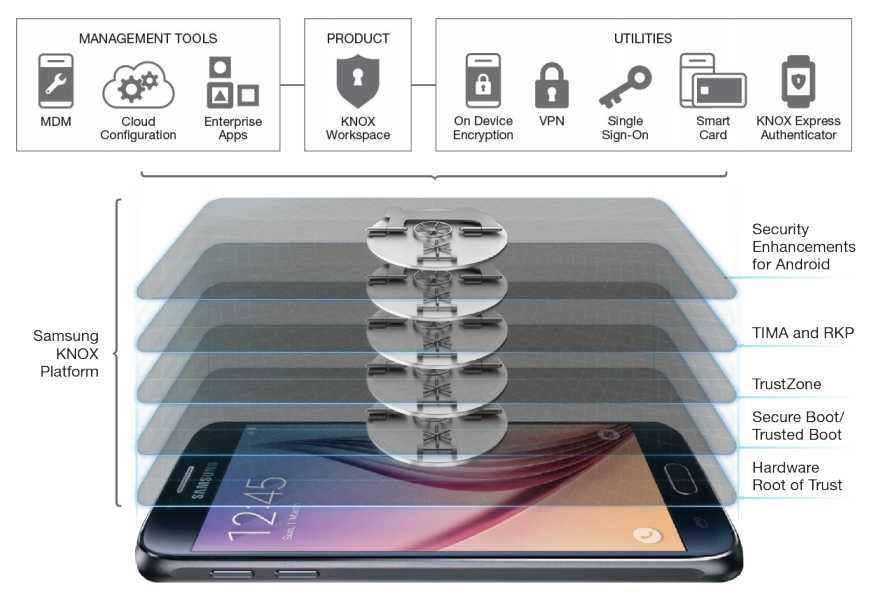
But ask him about how he uses Samsung Knox, the virtualization layer that cleanly separates work data from personal data on Samsung’s Android devices, and he’s happy to elaborate on his experience with it in his current and previous roles. The U.S. Department of Defence helped guide Samsung to meet the required compliance criteria to allow for Knox-enabled devices to become the first consumer mobile devices validated to all levels of classified material.

To do so, Knox meets the Mobile Operating System Security Requirements Guides published by the Defense Information Systems Agency and the Federal Information Processing Standards as authored by the National Institute of Standards and Technology. Those credentials have proved good enough to gain cross-border credibility in Canada too, with Halvorsen helping the federal government implement Knox.
Pulling his current Samsung Galaxy device out of the pocket of his suit jacket, the veteran CIO shares how Samsung is drinking its own champagne and making use of Knox internally.
“It can be your personal cell phone and the container allows it to be your business cell phone,” he says. “It gives both the employee and the employer some benefits.”
Knox’ container system – a sort of virtual data bubble that separates one mobile device into different user profiles with different apps, files, and permissions – can support two different work-based containers. On Halvorsen’s phone for example, three different containers are deployed representing his role within Samsung’s larger organization – there’s the container for Samsung Electronics of America, the global Samsung corporate container, and his own personal and open container.
“As you go up higher in the organization, there is more material that’s more restricted and they are less willing to share,” he explains.
The Knox platform makes use of the Secure Element for Android Management Service, which provides high control over the operating system’s security policy engine. This allows organizations to tailor different software permissions, isolating applications and data dynamically. It could also allow professionals that have multiple employers to use their own device to interact with different organizations (think of a consultant that spends time with two different firms.)
Knox can also offer administrators finer control over other camera functions, aside from data delineation. The camera could be locked in certain situations, for example, to ensure that employers around classified documents can’t steal the information with a simple photo. Halvorsen points out that these adjustments can also be made through a cloud dashboard.
Knox admins can also enable NFC and Bluetooth functions inside the Workspace containers. That allows the NFC chip to act like a SmartCard-based credential system, allowing employers physical access to different rooms with their smartphones. Bluetooth can be honed to enable printing, file sharing, and connection to a range of external devices.
While it’s certified for the Pentagon, Knox’s security record isn’t totally spotless. In 2016, Israeli researchers uncovered three key vulnerabilities in Knox. According to a research paper, these vulnerabilities could, in theory, be exploited to decrypt user data without a password, run a man in the middle attack on SSL traffic, or scoop data from the Knox clipboard. These patches have long since been patched by Samsung.
The Israeli team was using sophisticated attack methods, Halvorsen says. “It’s not the attacks that 80 per cent of the people conducting attacks are even using.”
Given that data is “the most valuable resource on the Earth today,” Halvorsen says Samsung is focused on staying one step ahead of hackers. It might not be perfect, but no system is.
“There’s no system that’s 100 per cent secure today,” he says. “Knox is one of the most secure systems out there.”
Halvorsen recalls that before he became a Knox users at the Department of Defence in 2014, he was accustomed to carrying around multiple devices. When changes needed to be made, a phone had to be dropped off overnight with the IT desk.
“Before you were carrying four different phones and this at least lets you get rid of all but one of them,” he says. “Today with Knox, the provisioning can be done more and more over the air. It allows us to update systems more frequently and collect more data.”
It sounds like the sort of security that’s fit for the President. But don’t ask Halvorsen about it.
